Establishing a global security operations center is an essential investment in your organization's security. Learn more about the benefits of an outsourced solution and how to choose the right provider.
|
Updated: September 19, 2024 INSIDE THIS ARTICLE, YOU'LL FIND: |
Now more than ever, businesses and their employees face ongoing challenges from increasingly sophisticated physical and digital threats. The responsibility of safeguarding people, sensitive data, and critical assets has never been more crucial – or more demanding. Unfortunately, not every company has the resources or budget to develop a full-time threat detection and response effort, even as their business scales.
Amid this challenging landscape, many organizations are turning to an innovative solution: outsourcing their security operations, typically to what’s called a security operations center (SOC) or a global security operations center (GSOC). Working with an experienced GSOC partner is a powerful way for businesses to fortify their defenses against modern threats.
In this guide, we'll explore the benefits of GSOC as a service, and how it empowers businesses to navigate the evolving landscape with confidence and resilience.
What is a GLOBAL Security Operations Center?
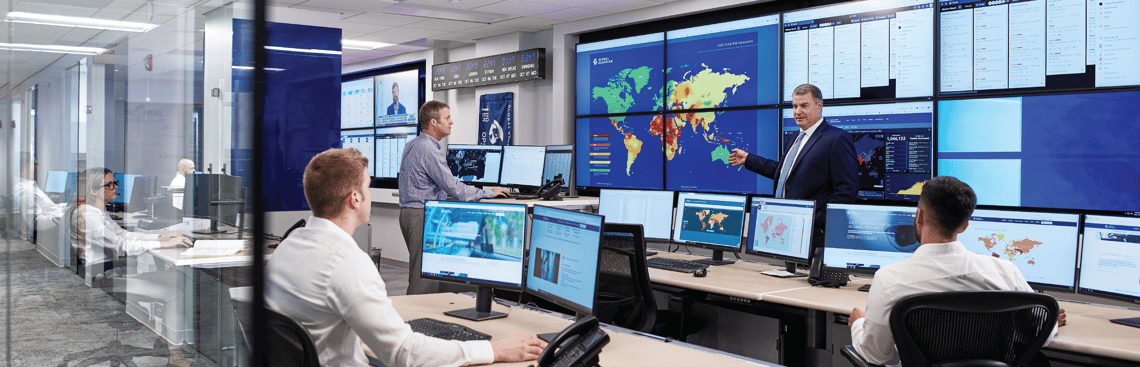
A GSOC or SOC is a centralized unit responsible for monitoring, detecting, and responding to security incidents and threats across an organization's infrastructure. It acts as the nerve center for security operations, providing real-time insights into potential risks and enabling timely responses to mitigate security breaches.
GSOCs oversee various security measures and functions for an organization, including physical security, video surveillance, and cybersecurity. A GSOC is imperative for organizations that need to protect personnel as part of their travel risk management program: GSOCs provide global threat monitoring, intelligence-informed operations, mass communications, individual wellness checks, geofencing, and on-demand security support capabilities that help safeguard people wherever they go on behalf of their business.
This integration of every aspect of security, rolled into one holistic unit, allows an elite GSOC to comprehensively protect and support their team or clients.
What is a VSOC?
A VSOC (Virtual Security Operations Center) is a cloud-based solution that provides security monitoring and threat response services without the need for a physical facility. It leverages remote technologies, allowing security professionals to monitor and manage operations from various locations.
VSOCs primarily focus on cybersecurity, utilizing advanced tools like artificial intelligence and machine learning to detect and respond to digital threats. They are well-suited for companies that prioritize cyber risk management over physical security systems, though they may offer some crossover capabilities. This is a different model from outsourcing your GSOC, where an external provider manages your entire security operations.
Why Companies Outsource Their GSOC
There are many reasons why a company would choose to go with a managed or outsourced GSOC, rather than building their own apparatus.
Outsourcing provides a solution for those without an internal SOC or for companies seeking to complement existing SOC efforts. And what does that solution provide? Here are a few of the most common reasons cited by those who opt for outsourcing a GSOC:
- Speed and ease of setup: Building an in-house GSOC can take up to a year or more, whereas outsourcing allows businesses to set up a fully operational GSOC much faster. Speed and ease are particularly appreciated by startups and businesses in high-growth mode.
- Talent and expertise gaps: Many in-house GSOCs are staffed by personnel who transitioned from the physical guarding sector, leading to a skill gap as it relates to applying intelligence and operating proactively to mitigate threats. Outsourcing a GSOC ensures access to a workforce with an extensive and specialized skillset and background.
- Lack of standards in GSOCs: Without a regulatory body or governing standards, many in-house GSOCs lack clear best practices. GSOC providers, however, have established expertise in developing standard operating procedures (SOPs) and ensuring that operations meet industry norms and compliance requirements.
- Comprehensive security strategy: Outsourced GSOCs provide more than just monitoring — they offer access to security strategy development. With a team of experts, businesses can rely on their GSOC provider to craft and execute a cohesive security strategy tailored to their needs.
- Cost-effectiveness and scalability: Outsourcing a GSOC is often more cost-effective than building and maintaining an in-house center, as it reduces the financial burden of managing large security budgets and expensive technology while still providing access to advanced tools. This cost-effectiveness is important especially when an organization needs to scale its security operations, as the operations can grow and change to meet the organization’s needs.
- Focus on core business operations: By outsourcing their GSOC, businesses can free up their internal IT and security teams to concentrate on core business operations instead of constantly managing security monitoring and incident response.
Comparing Managed GSOC Services vs. In-house GSOC
While outsourcing offers many advantages, some organizations may prefer an in-house GSOC. Having an internal team may provide a deeper level of customization, aligning the GSOC's processes precisely with the organization's unique security needs and industry regulations. This level of control can be especially crucial for companies operating in highly regulated sectors with specific compliance requirements.
However, there are higher initial investments and ongoing costs associated with building and maintaining an in-house GSOC. Apart from the considerable upfront expenses, businesses must allocate resources for training, upgrades, and staying informed about evolving threats, as well as heavy infrastructure costs such as valuable real estate. For smaller organizations or those without dedicated security expertise, this can be a significant challenge.
Additionally, GSOC providers like Global Guardian can stand up and run the equivalent of in-house GSOCs for a client. Rather than the business investing on-going time and resources in maintaining their own GSOC, a provider can bring their expertise to running such an operation to the business — mitigating many of the benefits that creating one’s own GSOC would ostensibly bring in terms of integration and collaboration. The team can work closely with other departments, fostering collaboration and facilitating faster information sharing during security incidents.
By leveraging a managed GSOC, businesses can take advantage of a flexible model, paying for the services they need as they need them. This scalability allows businesses to tailor their security operations to match their requirements, making it an attractive option for organizations of all sizes.
In summary, a GSOC or SOC can take several forms. It can be a third-party command center that integrates with your existing organizational structure and handles all requests and emergencies; it can also be an in-house team that you either set up yourself or invite aboard to work more directly with the broader business. Either way, make sure that you’re working with a best-in-class team, as the safety of your people and assets is always the paramount concern.
How to Choose a GSOC Service Provider
Choosing the right GSOC service provider is a critical decision that can significantly impact your organization's security posture. This can include everything from how you plan and manage corporate travel, to monitoring your physical assets, to protecting your employees or leadership team when they’re at the office or on the go.
To ensure you make the best choice, consider the following key factors when evaluating potential GSOC service providers:
- Alignment with business requirements and goals: Clearly define your organization's security needs and objectives. Are you seeking 24-hour response and protection, asset surveillance, cybersecurity, executive protection and transportation? Assess your current security infrastructure and determine what specific services and capabilities you require from a GSOC provider. Understanding your goals will help you find a provider whose offerings align with your unique security requirements.
- Expertise and experience: Research the track record, certifications, and experience of GSOC service providers being considered. An outsourced GSOC should have analysts with strong academic backgrounds, specialized skills (such as intelligence, threat hunting and monitoring), and fluency in multiple languages.
- Proactive intelligence: An outsourced GSOC can identify emerging vulnerabilities through constant threat hunting and proactive intelligence, allowing organizations to implement preventative measures effectively, while offering immediate response in the event of a threat.
- Technology infrastructure: Ensure that the GSOC provider utilizes advanced technologies and tools to effectively monitor and detect potential threats. Inquire about the systems and processes they employ to analyze security data and how they stay current with emerging security trends.
- Elite data privacy and security measures: Data security is of paramount importance when selecting a GSOC provider. Verify that the provider follows strict data protection practices and regulations (such as GDPR, the Gramm-Leach-Bliley (GLB) Act, or the HIPAA Privacy Rule), and employs robust security measures to safeguard your sensitive information.
- Wide response network: A GSOC provider must do more than provide information and intelligence – it should also be able to tap into a worldwide response network to help execute on behalf its clients wherever their travel takes them.
Choosing the right GSOC solution is an essential investment in your organization's security. Take the time to conduct thorough research, consider your specific needs, and assess potential providers' capabilities to ensure a successful and long-term partnership. A well-chosen GSOC service provider will offer enhanced protection, enabling your business to operate confidently in an ever-changing threat landscape.
One such reputable GSOC provider is Global Guardian. With a proven record of accomplishment in managing GSOCs for diverse clientele, Global Guardian offers comprehensive security solutions backed by a team of highly skilled security experts. Utilizing advanced technology infrastructure, proactive threat detection, and round-the-clock monitoring, Global Guardian can tap into its teams in over 140 countries to respond to emergencies in real time – ensuring robust defense against risks.
Whether you opt for Global Guardian or another trusted GSOC provider, remember that outsourcing your GSOC empowers your business with cost-effective access to specialized expertise and state-of-the-art security technologies. This strategic move allows you to focus on your core operations while having peace of mind that your people and assets are well-protected.
Standing by to Support
The Global Guardian team is standing by to support your security requirements. To learn more about our Global Security Operations Center services and how we've supported clients in the protection of their assets, employees, and digital infrastructure, complete the form below or call us at + 1 (703) 566-9463.



